チェックポイント
Key Generation and Encryption
/ 20
Service Account and Workload Identity Pool
/ 30
Create the Blockchain Node and Results Bucket
/ 20
Create the MPC Instance
/ 15
Create the MPC Operator Confidential Space Instance
/ 15
Transacting Digital Assets with Multi-Party Computation and Confidential Space
GSP1128
Overview
In this lab, you will go through a reference implementation for MPC-compliant blockchain signing using Confidential Space. Let’s imagine Company A, which wants to transfer digital assets to Company B. Since they are leveraging an MPC-compliant model, instead of individual private keys, they use distributed key shares where key shareholders (Alice and Bob) collaborate to sign a transaction. This gives Company A the benefits of simplifying the user experience, and creating operational efficiencies, while retaining control over their private keys.
To describe the critical components that make this possible, you will walk through the technical setup, and outline the approval and signing process that triggers the transfer of digital assets from Company A to Company B. Please note that Bob and Alice work for Company A, and are required to approve the transaction.
This reference implementation covers signature operation, but does not cover all the aspect of MPC key management. For example, key generation will not be covered in this lab. Also, alternatives and complementary approaches exist – including using non-Google Cloud services for producing co-signatures, or having co-signers take turns to build the blockchain signature in their own environments (which is a more decentralized architecture).
In this lab, you will build the foundation for this interaction with a simple workload that signs an Ethereum transaction in Confidential Space based on co-signer key materials. First, you configure the necessary Cloud resources. Then, you run the workload in Confidential Space.
Objectives
In this lab, you will learn how to perform the following tasks:
- Learn about Confidential Space
- Create an Ethereum private test network
- Create a Confidential Space VM
- Interact with Ethereum from the Confidential Space VM
- Create and manage Workload Identity Pools
- Sign and submit an Ethereum transaction using Confidential Space
Setup and requirements
Before you click the Start Lab button
Read these instructions. Labs are timed and you cannot pause them. The timer, which starts when you click Start Lab, shows how long Google Cloud resources will be made available to you.
This hands-on lab lets you do the lab activities yourself in a real cloud environment, not in a simulation or demo environment. It does so by giving you new, temporary credentials that you use to sign in and access Google Cloud for the duration of the lab.
To complete this lab, you need:
- Access to a standard internet browser (Chrome browser recommended).
- Time to complete the lab---remember, once you start, you cannot pause a lab.
How to start your lab and sign in to the Google Cloud console
-
Click the Start Lab button. If you need to pay for the lab, a pop-up opens for you to select your payment method. On the left is the Lab Details panel with the following:
- The Open Google Cloud console button
- Time remaining
- The temporary credentials that you must use for this lab
- Other information, if needed, to step through this lab
-
Click Open Google Cloud console (or right-click and select Open Link in Incognito Window if you are running the Chrome browser).
The lab spins up resources, and then opens another tab that shows the Sign in page.
Tip: Arrange the tabs in separate windows, side-by-side.
Note: If you see the Choose an account dialog, click Use Another Account. -
If necessary, copy the Username below and paste it into the Sign in dialog.
{{{user_0.username | "Username"}}} You can also find the Username in the Lab Details panel.
-
Click Next.
-
Copy the Password below and paste it into the Welcome dialog.
{{{user_0.password | "Password"}}} You can also find the Password in the Lab Details panel.
-
Click Next.
Important: You must use the credentials the lab provides you. Do not use your Google Cloud account credentials. Note: Using your own Google Cloud account for this lab may incur extra charges. -
Click through the subsequent pages:
- Accept the terms and conditions.
- Do not add recovery options or two-factor authentication (because this is a temporary account).
- Do not sign up for free trials.
After a few moments, the Google Cloud console opens in this tab.

Activate Cloud Shell
Cloud Shell is a virtual machine that is loaded with development tools. It offers a persistent 5GB home directory and runs on the Google Cloud. Cloud Shell provides command-line access to your Google Cloud resources.
- Click Activate Cloud Shell
at the top of the Google Cloud console.
When you are connected, you are already authenticated, and the project is set to your Project_ID,
gcloud is the command-line tool for Google Cloud. It comes pre-installed on Cloud Shell and supports tab-completion.
- (Optional) You can list the active account name with this command:
- Click Authorize.
Output:
- (Optional) You can list the project ID with this command:
Output:
gcloud, in Google Cloud, refer to the gcloud CLI overview guide.
Task 1. Key Generation and Encryption
- Open Cloud Shell and run the following command to set the project ID:
You can check this was properly set by running:
You'll be using this variable throughout the remainder of the lab.
- Run the following command to enable the APIs that will be used in the lab:
Create the encryption keyring in KMS for the private key
In this section you will create the encryption key which will be used to encrypt the private key shares.
- Create the key ring. After running the below command, you might need to enter
yto enable the API.
- Create the KMS key.
- Grant your user account access to the key to encrypt the keys.
Create the Ethereum private key
For this lab, you'll be using this private key: 0000000000000000000000000000000000000000000000000000000000000001. In a production scenario, you'd generate your own private key. If you'd like to use a different private key for the lab be sure to include it in the CLI flag below when running the Ganache VM. You are now going to split your private key into two shares and encrypt each.
- Add your private key to a gcloud file for encryption:
- Then run the command to store Bob's private key share.
Encrypt the Ethereum private key shards using KMS
- Encrypt Alice's private key share.
- Encrypt Bob's private key share.
Create the bucket to store the encrypted keys
The mpc-encrypted-keys bucket will store the encrypted keys of Alice and Bob. In a production application, these keys could be held by Alice and Bob and then handed over when approval by each party is granted. They could also be separated out into different buckets on different projects.
- Create the
mpc-encrypted-keysbucket.
- Upload Alice's and Bob's encrypted keys into the bucket. By doing this, we're approving the transaction and granting the Confidential Space VM access to the encrypted key.
Now that the keys have been created and encrypted, you can move on to the next step to create the MPC application.
Click Check my progress to verify the objective.
Task 2. Service Account and Workload Identity Pool
Create the MPC Service Account
- Create the trusted-mpc-account service account.
- Allow the MPC service account access to decrypt the key shards.
Create a Workload Identity Pool
We want to authorize workloads to access the encrypted keys based on attributes of the following resources.
- What: Code that is verified
- Where: An environment that is secure
- Who: An operator that is trusted
We use Workload identity federation to enforce an access policy based on these requirements.
Workload identity federation allows you to specify attribute conditions. These conditions restrict which identities can authenticate with the workload identity pool (WIP). You can add the Attestation Verifier Service to the WIP as a workload identity pool provider to present measurements and enforce the policy.
To create the WIP, complete the following steps.
CLI
- Create a WIP.
You will now create a new OIDC workload identity pool provider. The specified --attribute-condition authorizes access to the mpc-workloads container. It requires:
-
What: Latest
initial-workload-containeruploaded to thempc-workloadsrepository. - Where: Confidential Space trusted execution environment, version 0.1 or later.
-
Who: MPC
trusted-mpcservice account.
int(assertion.swversion) >= 1 to int(assertion.swversion) ==0 if you choose confidential-space-debug image when creating the instance in the later step. See here for the full list of confidential vm attribute conditions.
- Create the new OIDC workload identity pool provider.
- Grant the
workloadIdentityUserrole on thetrusted-mpc-accountservice account to thetrusted-workload-poolWIP. This allows the WIP to impersonate the service account.
Create run-confidential-vm service account
Create the run-confidential-vm service account.
CLI
- Create the run-confidential-vm service account.
- Grant the Service Account User role on the run-confidential-vm service account to your user account. This allows your user account to impersonate the service account.
- (Optional) Grant the service account the Log Writer permission. This allows the Confidential Space environment to write logs to Cloud Logging in addition to the Serial Console, so you can review logs after the VM is terminated (Requires
Security Adminpermission).
Click Check my progress to verify the objective.
Task 3. Create the Blockchain Node and Results Bucket
Ganache Ethereum Node
- Create the Ethereum Ganache instance and take note of the IP address. After running the below command, you might need to enter
yto enable the API.
Create a bucket for results
Create the $MPC_PROJECT_ID-mpc-results-storage bucket. Then grant the
run-confidential-vm service account permission to create files in the bucket,
so it can store the workload results there.
CLI
- Create the
mpc-results-storagebucket.
- Grant the Storage Object Creator role on the
/$MPC_PROJECT_ID-mpc-results-storagebucket to therun-confidential-vmservice account. This permits the service account to store query results to the bucket.
- Grant the Storage Object Viewer role on the
/$MPC_PROJECT_ID-mpc-encrypted-keysbucket to thetrusted-mpc-accountservice account. This permits the service account to view the encrypted keys that were added by Alice and Bob.
Click Check my progress to verify the objective.
Task 4. Create the MPC Instance
Create the files in the editor
- In Cloud Shell, click the
button to launch the Cloud Shell Editor.
You'll then find yourself in an IDE environment similar to Visual Studio Code, in which you can create projects, edit source code, run your programs, etc. If your screen is too cramped, you can expand or shrink the dividing line between the console and your edit/terminal window by dragging the horizontal bar between those two regions.
You can switch back and forth between the Editor and the Terminal by clicking the Open Editor and Open Terminal buttons, respectively. Try switching back and forth between these two environments now.
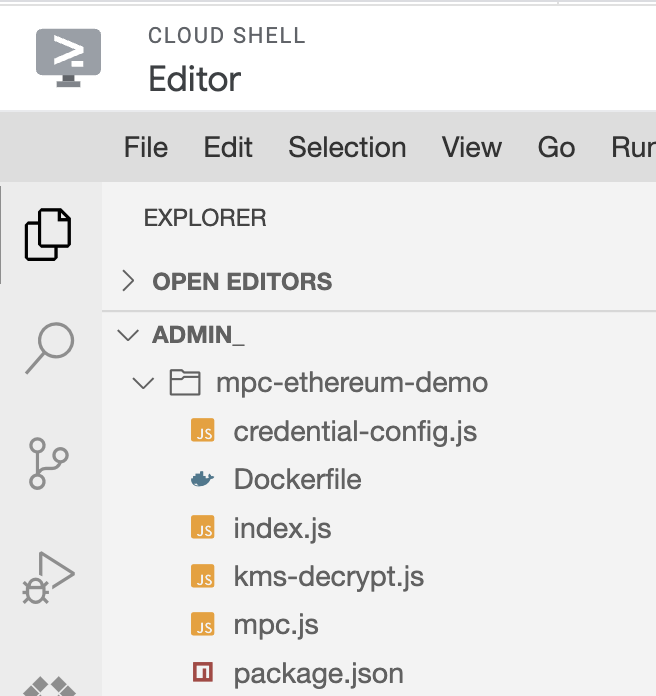
- Start by creating a folder in which to store your work for this lab, by selecting File > New Folder, enter
mpc-ethereum-demo, and click OK. All of the files you create in this lab, and all of the work you do in Cloud Shell, will take place in this folder.
package.json
-
Now create a
package.jsonfile. In the Cloud Editor window, click the File > New File menu to create a new file. When prompted for the new file's name, enterpackage.jsonand press the OK button. Make sure the new file ends up in thempc-ethereum-demoproject folder. -
Place the following code into the package.json file. This will tell our image what packages should be used for the mpc application. In this case, we're using the
@google-cloud/kms,@google-cloud/storage,ethers, andfast-crc32clibraries.
index.js
- Next, create a
index.jsfile and paste the following code into the file. This is our entry file that specifies what commands should be run when the image starts up. We've also included a sample unsigned transaction. This transaction would normally be coming from an untrusted application that asks users for their signature. Thisindex.jsfile also imports functions frommpc.js, which we'll be creating next.
mpc.js
- Create the
mpc.jsfile and paste the following code into the file. This is where the MPC signing will occur. We'll be importing functions fromkms-decrypt.jsandcredential-config.js, which we'll be creating next.
kms-decrypt.js
- Create the
kms-decrypt.jsfile and paste the following code into the file. This is where the decryption of the encrypted key shares will occur. We'll be importing functions fromcredential-config.js, which we'll be creating next.
credential-config.js
- Create the
credential-config.jsfile and paste the following code into the file. This is where the workload identity pool paths are stored and the service account impersonation will occur. We'll be importing functions fromcredential-config.js.
Dockerfile
- Lastly, you'll create your Dockerfile. Create the
Dockerfilefile and paste the following code into the file.
tee.launch_policy.allow_cmd_override"="true" in the Dockerfile is a launch policy set by the image author. It allows the operator to override the CMD when executing the workflow later. By default, allow_cmd_override is set to false. LABEL "tee.launch_policy.allow_env_override"tells Confidential Space which variables are allowed in the image.
Once all the files are created, it should look like:
Create the repository
- Click Open Terminal to re-open the Cloud Shell terminal. Run the following command to create the Artifact Registry docker repository.
- Build and publish the Docker container.
You might need to hit Y to confirm the config file.
- Grant the service account that's going to run the workload the Artifact Registry Reader (
roles/artifactregistry.reader) role so it can read from the repository:
- Grant the workloadUser role to the service account
Click Check my progress to verify the objective.
Task 5. Create the MPC Operator Confidential Space Instance
In this section, you will create the Confidential VM instance.
The following variables have been added to the image:
-
NODE_URL: the URL of the Ethereum node that will process the signed transaction. -
RESULTS_BUCKET: the bucket that stores the mpc transaction result. -
KEY_BUCKET: the bucket that stores the mpc encrypted keys. -
MPC_PROJECT_NUMBER: the project number, used for the credential config file. -
MPC_PROJECT_ID: the project id, used for the credential config file.
- Run the following command to create the Confidential VM instance.
Check the Cloud Storage Results
You can view the transaction receipt in Cloud Storage. It might take a few minutes for Confidential Space to boot and for results to appear. You'll know the container is done when the VM is in the stopped state.
- Go to the Cloud Storage Browser page.
- Click
$MPC_PROJECT_ID-mpc-results-storage. - Click on the
transaction_receiptfile. - Click Download to download and view the transaction response.
Check the Ganache Blockchain Transaction
You can also view the transaction in the blockchain log.
- Go to the Compute Engine page.
- Click on the
mpc-lab-ethereum-nodeVM. - Click
SSHto open the SSH-in-browser window. - In the SSH window, enter
sudo docker psto see the running Ganache container. - Find the container ID for
trufflesuite/ganache:v7.7.3 - Enter
sudo docker logs CONTAINER_IDreplacing CONTAINER_ID with the ID fortrufflesuite/ganache:v7.7.3. - View the logs for Ganache and confirm that there is a transaction listed in the logs.
Click Check my progress to verify the objective.
Congratulations!
You created a confidential space VM and signed a blockchain transaction using multi-party computation! You can now use this same process to sign transactions for other blockchain applications.
Next steps/Learn more
Google Cloud training and certification
...helps you make the most of Google Cloud technologies. Our classes include technical skills and best practices to help you get up to speed quickly and continue your learning journey. We offer fundamental to advanced level training, with on-demand, live, and virtual options to suit your busy schedule. Certifications help you validate and prove your skill and expertise in Google Cloud technologies.
Manual Last Updated October 26, 2023
Lab Last Tested October 26, 2023
Copyright 2023 Google LLC All rights reserved. Google and the Google logo are trademarks of Google LLC. All other company and product names may be trademarks of the respective companies with which they are associated.
