GSP698

Overview
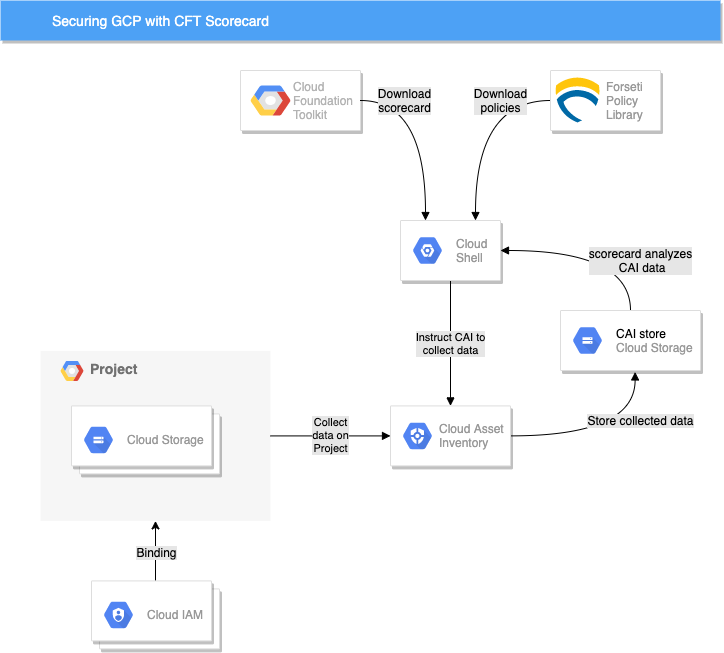
CFT Scorecard is an open-sourced command line client of Forseti Config Validator and part of the broader Cloud Foundation Toolkit. It provides visibility into misconfigurations and violations of an established set of standards for Google Cloud resources, projects, folders, or even organizations.
There are over 86 distinct Google Cloud resource types, and they're growing. With the move to public cloud, it is easier than ever to federate cloud operations and resource deployment out to many individuals. Along with federation and agility in the deployment of infrastructure, resources, and policy, it has become increasingly difficult to keep policies and standards in order.
In this lab you will configure CFT Scorecard to improve visibility into a Google Cloud project and detect misconfigurations.
What will you do in this lab?
This lab highlights the challenges with using the cloud with multiple concurrent users. You will enable the CFT Scorecard and extend its resource configuration monitoring and violation detection capabilities through integration with Cloud Asset Inventory and the open-sourced Policy Library. You will set up the tooling for detecting misconfigurations and over-exposed resources while still allowing other individuals within your team, and ultimately the Google Cloud project, to be agile within established policies.
Topics covered
- Setting up CFT Scorecard.
- Running a CFT Scorecard assessment.
- Adding new CFT Scorecard policy.
Scenario
Imagine you are the Technical Lead of a 3 person team. Your remote teammates, Alice and Bob, are working very closely with you and deploying many resources into the same shared Google Cloud project as you. After a few weeks of working together, you start to notice a few red flags. You soon discover that both Alice and Bob have cut corners and introduced project configurations that you consider misconfiguration. One misconfiguration exposed a Cloud Storage bucket publicly. This is merely one misconfiguration that you have uncovered, but you fear that there could be many more.
After doing a quick Google search, you come across the Cloud Foundation Toolkit (CFT) Scorecard CLI utility. After a quick read, you decide this can help you administer policies into your Google Cloud environment and determine where misconfigurations are occurring. You decide to give it a try.
Setup and requirements
Before you click the Start Lab button
Read these instructions. Labs are timed and you cannot pause them. The timer, which starts when you click Start Lab, shows how long Google Cloud resources are made available to you.
This hands-on lab lets you do the lab activities in a real cloud environment, not in a simulation or demo environment. It does so by giving you new, temporary credentials you use to sign in and access Google Cloud for the duration of the lab.
To complete this lab, you need:
- Access to a standard internet browser (Chrome browser recommended).
Note: Use an Incognito (recommended) or private browser window to run this lab. This prevents conflicts between your personal account and the student account, which may cause extra charges incurred to your personal account.
- Time to complete the lab—remember, once you start, you cannot pause a lab.
Note: Use only the student account for this lab. If you use a different Google Cloud account, you may incur charges to that account.
How to start your lab and sign in to the Google Cloud console
-
Click the Start Lab button. If you need to pay for the lab, a dialog opens for you to select your payment method.
On the left is the Lab Details pane with the following:
- The Open Google Cloud console button
- Time remaining
- The temporary credentials that you must use for this lab
- Other information, if needed, to step through this lab
-
Click Open Google Cloud console (or right-click and select Open Link in Incognito Window if you are running the Chrome browser).
The lab spins up resources, and then opens another tab that shows the Sign in page.
Tip: Arrange the tabs in separate windows, side-by-side.
Note: If you see the Choose an account dialog, click Use Another Account.
-
If necessary, copy the Username below and paste it into the Sign in dialog.
{{{user_0.username | "Username"}}}
You can also find the Username in the Lab Details pane.
-
Click Next.
-
Copy the Password below and paste it into the Welcome dialog.
{{{user_0.password | "Password"}}}
You can also find the Password in the Lab Details pane.
-
Click Next.
Important: You must use the credentials the lab provides you. Do not use your Google Cloud account credentials.
Note: Using your own Google Cloud account for this lab may incur extra charges.
-
Click through the subsequent pages:
- Accept the terms and conditions.
- Do not add recovery options or two-factor authentication (because this is a temporary account).
- Do not sign up for free trials.
After a few moments, the Google Cloud console opens in this tab.
Note: To access Google Cloud products and services, click the Navigation menu or type the service or product name in the Search field.

Activate Cloud Shell
Cloud Shell is a virtual machine that is loaded with development tools. It offers a persistent 5GB home directory and runs on the Google Cloud. Cloud Shell provides command-line access to your Google Cloud resources.
-
Click Activate Cloud Shell  at the top of the Google Cloud console.
at the top of the Google Cloud console.
-
Click through the following windows:
- Continue through the Cloud Shell information window.
- Authorize Cloud Shell to use your credentials to make Google Cloud API calls.
When you are connected, you are already authenticated, and the project is set to your Project_ID, . The output contains a line that declares the Project_ID for this session:
Your Cloud Platform project in this session is set to {{{project_0.project_id | "PROJECT_ID"}}}
gcloud is the command-line tool for Google Cloud. It comes pre-installed on Cloud Shell and supports tab-completion.
- (Optional) You can list the active account name with this command:
gcloud auth list
- Click Authorize.
Output:
ACTIVE: *
ACCOUNT: {{{user_0.username | "ACCOUNT"}}}
To set the active account, run:
$ gcloud config set account `ACCOUNT`
- (Optional) You can list the project ID with this command:
gcloud config list project
Output:
[core]
project = {{{project_0.project_id | "PROJECT_ID"}}}
Note: For full documentation of gcloud, in Google Cloud, refer to the gcloud CLI overview guide.
Task 1. Set up the environment
- Open Cloud Shell and set a couple of environment variables to begin:
export GOOGLE_PROJECT=$DEVSHELL_PROJECT_ID
export CAI_BUCKET_NAME=cai-$GOOGLE_PROJECT
- After reading the docs, understand that CFT scorecard has two dependencies:
- Cloud Asset Inventory
- Policy Library
- Proceed to enable Cloud Asset API in your project:
gcloud services enable cloudasset.googleapis.com \
--project $GOOGLE_PROJECT
- Run this command to create the default Cloud Asset service account:
gcloud beta services identity create --service=cloudasset.googleapis.com --project=$GOOGLE_PROJECT
- Grant the storage admin role to the cloud assets service account:
gcloud projects add-iam-policy-binding ${GOOGLE_PROJECT} \
--member=serviceAccount:service-$(gcloud projects list --filter="$GOOGLE_PROJECT" --format="value(PROJECT_NUMBER)")@gcp-sa-cloudasset.iam.gserviceaccount.com \
--role=roles/storage.admin
- Clone the Policy Library:
git clone https://github.com/forseti-security/policy-library.git
- You realize Policy Library enforces policies that are located in the policy-library/policies/constraints folder, in which case you can copy a sample policy from the samples directory into the constraints directory.
cp policy-library/samples/storage_denylist_public.yaml policy-library/policies/constraints/
- Create the bucket that will hold the data that Cloud Asset Inventory (CAI) will export:
gsutil mb -l {{{project_0.default_region | REGION}}} -p $GOOGLE_PROJECT gs://$CAI_BUCKET_NAME
Click Check my progress to verify the objective.
Create the CAI bucket
Task 2. Collect data using Cloud Asset Inventory (CAI)
Now that you have set up your environment, start collecting the data for CFT Scorecard.
As mentioned earlier, input to CFT Scorecard is resource and IAM data, and the policy-library folder.
You'll need to use CAI to generate the resource and IAM policy information for the project.
- Use the command below to create the data:
# Export resource data
gcloud asset export \
--output-path=gs://$CAI_BUCKET_NAME/resource_inventory.json \
--content-type=resource \
--project=$GOOGLE_PROJECT
# Export IAM data
gcloud asset export \
--output-path=gs://$CAI_BUCKET_NAME/iam_inventory.json \
--content-type=iam-policy \
--project=$GOOGLE_PROJECT
# Export org policy data
gcloud asset export \
--output-path=gs://$CAI_BUCKET_NAME/org_policy_inventory.json \
--content-type=org-policy \
--project=$GOOGLE_PROJECT
# Export access policy data
gcloud asset export \
--output-path=gs://$CAI_BUCKET_NAME/access_policy_inventory.json \
--content-type=access-policy \
--project=$GOOGLE_PROJECT
Example output:
Export in progress for root asset [projects/qwiklabs-gcp-01-68169ed6dd00].
Use [gcloud asset operations describe projects/97186664469/operations/ExportAssets/RESOURCE/2295255602305764396] to check the status of the operation.
Export in progress for root asset [projects/qwiklabs-gcp-01-68169ed6dd00].
Use [gcloud asset operations describe projects/97186664469/operations/ExportAssets/IAM_POLICY/11771734913762837428] to check the status of the operation.
- Ensure CAI has finished data collection. Look at the output from the previous command and use the provided
gcloud asset operations describe from the output of the above commands to verify these operations have finished. It might take some time to check the progress.
Click Check my progress to verify the objective.
Create the CAI files have been created
Task 3. Analyze CAI data with CFT scorecard
- You need to download the CFT scorecard application and make it executable:
curl -o cft https://storage.googleapis.com/cft-cli/latest/cft-linux-amd64
# make executable
chmod +x cft
- Now that you have configured everything, go ahead and run the CFT scorecard application:
./cft scorecard --policy-path=policy-library/ --bucket=$CAI_BUCKET_NAME
Example output:
Generating CFT scorecard
1 total issues found
Operational Efficiency: 0 issues found
----------
Security: 1 issues found
----------
denylist_public_users: 1 issues
- //storage.googleapis.com/fun-bucket-qwiklabs-gcp-00-2d8ed2a5cc0e is publicly accessable
Reliability: 0 issues found
----------
Other: 0 issues found
----------
This was the public bucket you identified earlier.
Task 4. Add more constraints to CFT scorecard
- You forgot about IAM! Add the following constraint to ensure you are entirely aware who has the
roles/owner role aside from your allowlisted user:
# Add a new policy to blacklist the IAM Owner Role
cat > policy-library/policies/constraints/iam_allowlist_owner.yaml << EOF
apiVersion: constraints.gatekeeper.sh/v1alpha1
kind: GCPIAMAllowedBindingsConstraintV3
metadata:
name: allowlist_owner
annotations:
description: List any users granted Owner
spec:
severity: high
match:
target: ["organizations/**"]
exclude: []
parameters:
mode: allowlist
assetType: cloudresourcemanager.googleapis.com/Project
role: roles/owner
members:
- "serviceAccount:admiral@qwiklabs-services-prod.iam.gserviceaccount.com"
EOF
- Rerun CFT scorecard:
./cft scorecard --policy-path=policy-library/ --bucket=$CAI_BUCKET_NAME
Ok, it all looks clean, but let's look at roles/editor, too.
- Set two extra variables to help with the new constraint creation:
export USER_ACCOUNT="$(gcloud config get-value core/account)"
export PROJECT_NUMBER=$(gcloud projects describe $GOOGLE_PROJECT --format="get(projectNumber)")
- Create the following constraint that will allowlist all the valid accounts:
# Add a new policy to allowlist the IAM Editor Role
cat > policy-library/policies/constraints/iam_identify_outside_editors.yaml << EOF
apiVersion: constraints.gatekeeper.sh/v1alpha1
kind: GCPIAMAllowedBindingsConstraintV3
metadata:
name: identify_outside_editors
annotations:
description: list any users outside the organization granted Editor
spec:
severity: high
match:
target: ["organizations/**"]
exclude: []
parameters:
mode: allowlist
assetType: cloudresourcemanager.googleapis.com/Project
role: roles/editor
members:
- "user:$USER_ACCOUNT"
- "serviceAccount:**$PROJECT_NUMBER**gserviceaccount.com"
- "serviceAccount:$GOOGLE_PROJECT**gserviceaccount.com"
EOF
- Rerun CFT scorecard:
./cft scorecard --policy-path=policy-library/ --bucket=$CAI_BUCKET_NAME
Example output:
Generating CFT scorecard
3 total issues found
Reliability: 0 issues found
----------
Other: 2 issues found
----------
identify_outside_editors: 1 issues
- IAM policy for //cloudresourcemanager.googleapis.com/projects/1044418630080 grants roles/editor to user:qwiklabs.lab.user@gmail.com
Operational Efficiency: 0 issues found
----------
Security: 1 issues found
----------
denylist_public_users: 1 issues
- //storage.googleapis.com/fun-bucket-qwiklabs-gcp-00-2d8ed2a5cc0e is publicly accessable
You should now see an editor who is not in your organization. Time to talk to Alice and Bob.
Congratulations!
You have learned how to download, set up, and use the CFT scorecard to analyze a Google Cloud project.
Google Cloud training and certification
...helps you make the most of Google Cloud technologies. Our classes include technical skills and best practices to help you get up to speed quickly and continue your learning journey. We offer fundamental to advanced level training, with on-demand, live, and virtual options to suit your busy schedule. Certifications help you validate and prove your skill and expertise in Google Cloud technologies.
Manual Last Updated April 12, 2024
Lab Last Tested April 12, 2024
Copyright 2025 Google LLC. All rights reserved. Google and the Google logo are trademarks of Google LLC. All other company and product names may be trademarks of the respective companies with which they are associated.










